WATERMARKING: WHAT IS IT AND WHY IS IT NEEDED?
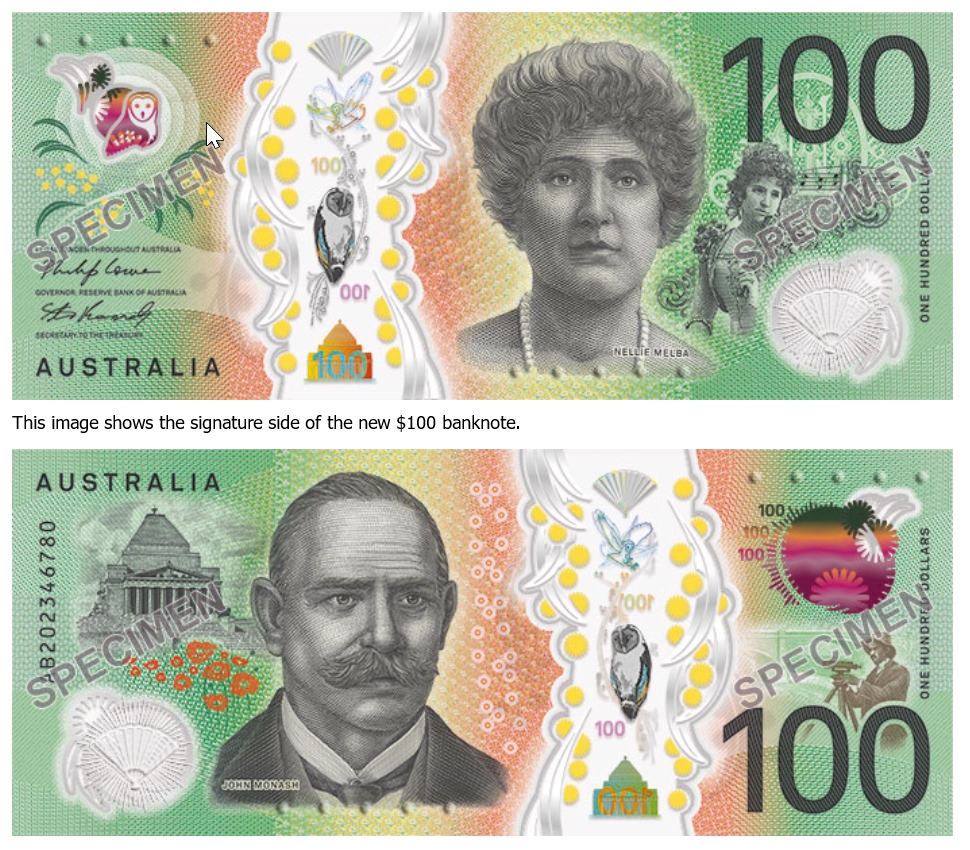
- A mark that is covertly inserted in an entity such as a paper document or a byte stream of an image/video is called a ‘watermark’, where this secretly embedded mark represents the ‘owner’ of an entity (refer to Fig. 1). The embedded mark is expected to not degrade and to not disturb the given functionality, information, quality, or data related to entity on which it is applied. In most cases, it is also expected to be imperceptible to human perception so that it does not divert attention from the main entity. The watermark should, but does not necessarily need to, contain a relation to the entity on which it is embedded [1, 2]. As depicted in Fig.2, popular watermarking entities are paper documents, bank notes, currency, postage stamps, images, audio and video clips, computer programs, hardware devices, and chips deployed in consumer electronics devices. Watermarks can be of two types: (a) regular or analog watermarks, or (b) digital (forensic) watermarks. Regular watermarks have existed for centuries in various forms, but digital watermarks came into existence in the last decade or so. Digital watermarks differ from regular watermarks in terms of perceptibility to human senses; they are only perceptible to humans only after some logical processing. In most cases, regular watermarks remain easily perceptible by humans and are difficult to remove or tamper with without degrading the entity.
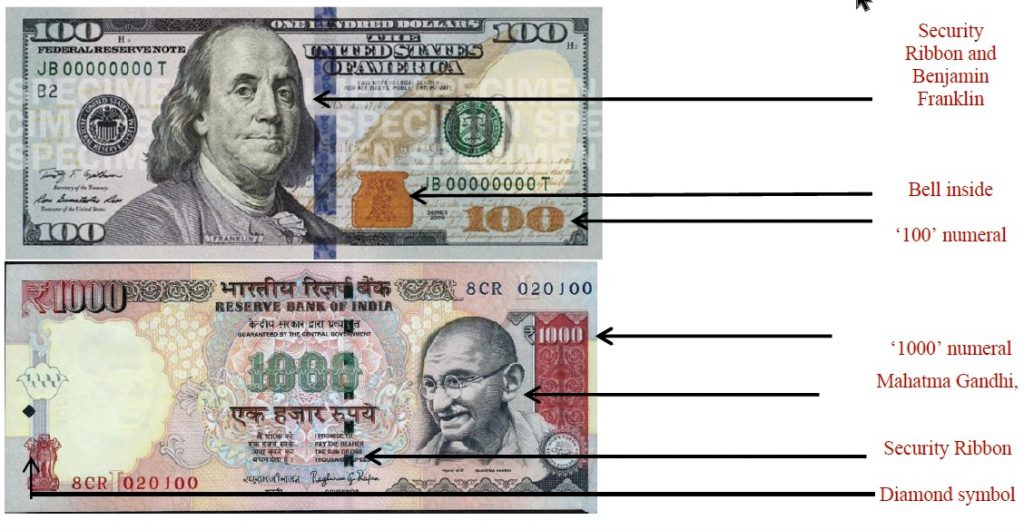
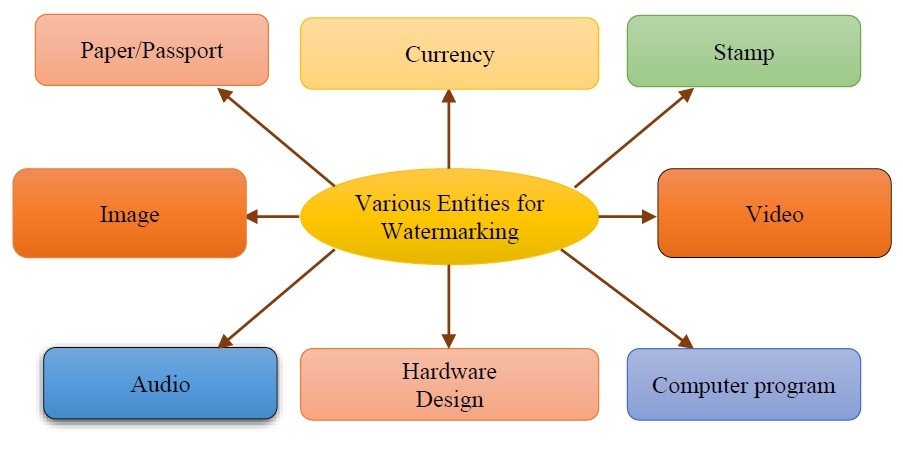
FIGURE 2 . Various watermarking
- The term ‘watermarking’ refers to the process of embedding a hidden mark of an owner in an entity for resolving any ownership conflicts that may arise. Thus, the main goal of a watermark is to protect a genuine owner against illegal claims of ownership, illegal distribution of copyrighted works, piracy and forgery or theft. Creative entities, irrespective of their complexity, have always been susceptible to theft and copyright infringement. Hence, formal mechanisms are required to safeguard a genuine owner from external malicious attacks. It may be noted here that watermarking does not aim to prevent malicious attacks such as infringements, illegal claims of ownership, piracy etc., but provides a strong formal mechanism to track/detect such illegal activities and potentially identify the perpetrators of such activities.
In order to protect against product counterfeiting and to secure its information, an ongoing and continuous development and improvement of the security features is required. To provide reliable protection against counterfeiting, various security features are added to the surface or directly into the paper structure during the manufacturing process. The most common security features include watermarks, use of security fibers, chemical protection and application of holograms.
Protective elements are subdivided into elements visible to the eye, further elements recognizable only under special detection device (such as a security fiber visible only under UV light) and elements verifiable on the laboratory level, for example, securing security papers using own DNA, allowing the paper to be verified even after burning.
Production presentation.
The best way of protecting documents against counterfeiting is to use security paper and security printing.
In practical application, Security papers are used for the production of security products, such as:
– notes, bills, stock exchange certificates, bonds, share certificates, stamps, food stamps, tickets, diplomas and report cards, documents and papers of national importance presenting a certain financial value, etc.
Currently, our company produces more than 1,000 types of security paper products having different technical specification. The paper is produced as wood-free, using either cellulose or cotton fibers.
With paper money, the materials are as important as the manufacturing process in producing the final product. The paper, also known as the substrate, is a special blend of 75% cotton and 25% linen to give it the proper feel. It contains small segments of red /blue/others color fibers scattered throughout for visual identification. Starting in 1990, the paper for $10 bills and higher denominations was made of two plies with a polymer security thread laminated between them. The thread was added to $5 bills in 1993. This thread is visible only when the bill is held up to a light and cannot be duplicated in photocopiers or printers.
Distribution of protective elements:
Security features in paper structure
Security features in paper structure are very difficult to counterfeit. The most common security features are watermarks, security fibres, or the use of chemical protection.
Security features on paper surface
The most commonly used protective elements on the paper surface are applications of holograms or holographic film.
Security Printing
In order to achieve reliable level of security during the printing process, a combination of several printing techniques, special colors and paints are being used, which may be, for example, be visible only under UV lamp. Typical security printing technologies include registration marks, variable ink, hidden pattern guilloches, micro-text, anti-copy color, etc.
The process of embedding a watermark in a document can be accomplished in two ways: (a) via the dandy roll process, or (b) via the cylinder mold process. In the first method (shown in Fig.3), a watermark is created by impressing a water coated metal stamp or dandy roll onto the paper during the manufacturing process. The dandy roll is a light roller which is covered by a material similar to the one used in a window screen that is imprinted with a pattern, i.e. a mesh like material with a specific design engraved. The still wet reel of paper (pulp) flows under the dandy roll which then imprints by pressure on the paper the designed watermark. The imprint pattern on the dandy roll is typically comprised of a laid wire that runs in parallel to the axis of the dandy roll, and a chain wire that runs around the circumference of the roll. The laid wire imprints light marks on the wet paper while the chain wire produces a strong imprint on the pulp while manufacturing.
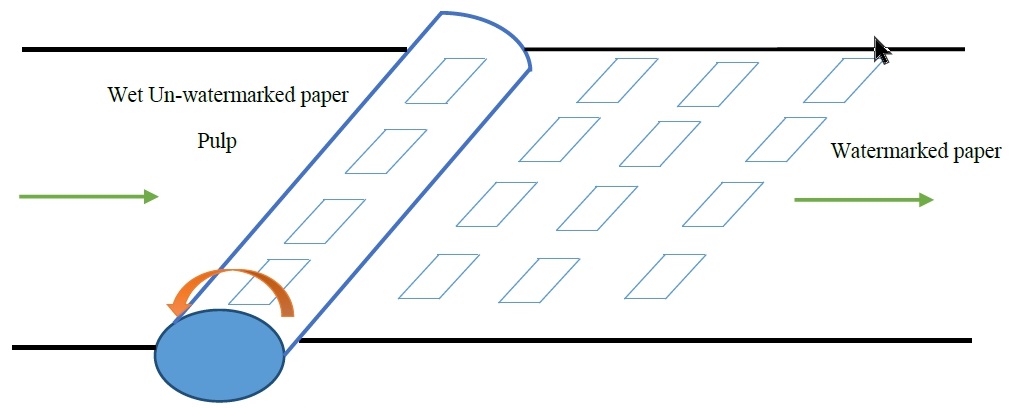
Fig 3. Dandy roll watermarking process
The cylinder mold watermarking method, on the other hand, creates a light to dark shaded imprint resembling a 3D image on the paper. This image is created by areas of relief on the roll itself. This watermarking process is extremely complex, and makes the reproduction of watermarks very challenging, Specifically, the reproduction complexity of watermarks produced by this method is due to the following reasons: (i) the extremely time consuming nature of the process, (ii) the high degree of skill and resources required for watermark creation, and (iii) the requirement of thorough knowledge about the process for creation of watermarks. However, when the costly equipment is available, the process turns out to be simple yet robust. Hence, this process is very frequently used for watermarking of bank notes/currencies, postal stamps and passports to protect the genuine owners/creators from counterfeits/forgery. An example of watermark insertion in bank notes is shown in Fig4.